Trusted Platform Module (TPM)
A TPM is a specialized chip soldered on an endpoint device’s motherboard that provides hardware-based device authentication, tamper detection, and encryption key storage.
The TPM generates RSA encryption keys specific to the host system making it impossible to recover data from an encrypted hard drive in a different computer than the one in which it was originally installed.
Further, the TPM generates a unique digital signature from the motherboard in which it was originally embedded, foiling any attempts to move the TPM chip itself to another machine.
This secure cryptographic integrated circuit provides a hardware-based approach to manage user authentication, network access and data protection. The TPM can be used with any major operating system and works best in conjunction with other security technologies such as firewalls, antivirus software, smart cards and biometric verification.
Secure Boot
When you boot a modern Windows PC, the Secure Boot feature in the UEFI firmware checks the operating system loader and its drivers to ensure they’re signed by an approved digital signature. On Windows PCs, the UEFI Secure Boot feature generally checks to see if the low level software is signed by Microsoft or the computer’s manufacturer. This prevents low-level malware like rootkits from interfering with the boot process. Note that the latest versions of popular Linux distributions, including Ubuntu, Mint and Fedora, already install just fine on a Windows PC that has Secure Boot enabled.
Besides, Linux operating systems can now take advantage of secure boot in Generation 2 VMs in Hyper-V on Windows 10. Both Ubuntu 14.04 and SUSE Linux Enterprise Server 12 are currently supported, and this trend will widen over time. These Linux VMs must be configured to use the Microsoft UEFI Certificate Authority (CA) as a Secure Boot template. 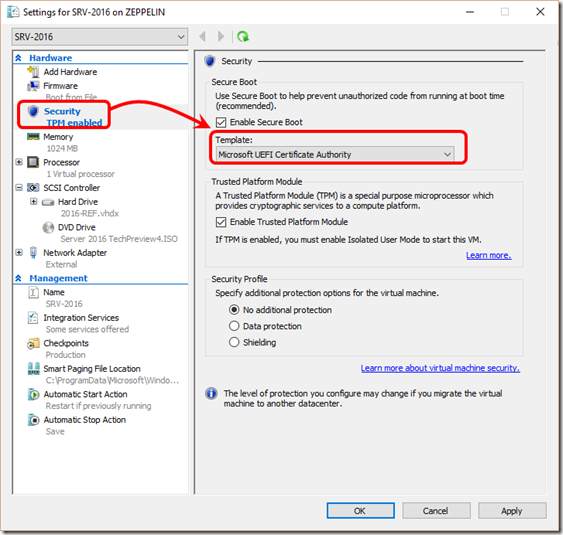
Measured Boot
One of the most concerning trends in malware over the last few years is the appearance of increasingly sophisticated rootkits that can hide from detection. In order to detect and resolve these early boot threats, Windows 8 introduced a new feature called Measured Boot, which measures each component, from firmware up through the boot start drivers, stores those measurements in the TPM on the machine, and then makes available a log that can be tested remotely to verify the boot state of a client machine.
The Measured Boot feature provides antimalware software with a reliable (resistant to tampering and spoofing) log of all boot components that started before the antimalware software. Thus, the software can use the log to determine whether components that ran before it are trustworthy or if they are infected with malware.
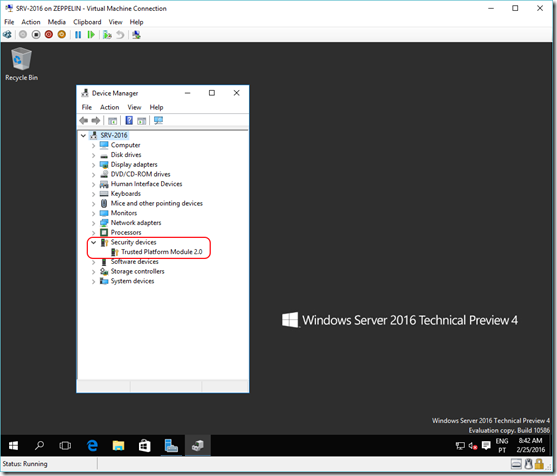
Virtual TPM on Windows 10 Hyper-V
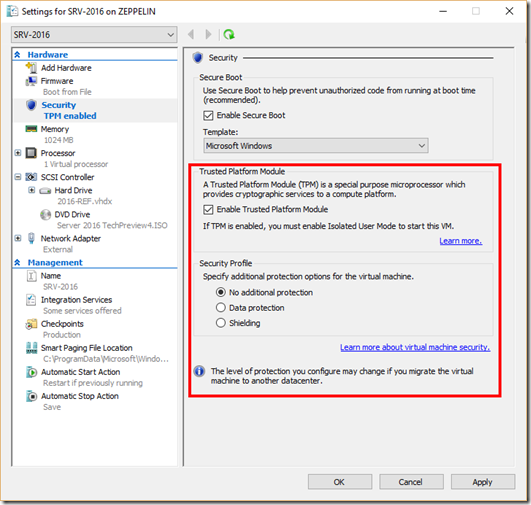
Windows 10 version 1511 (Fall Update) brought a number of new features to Microsoft’s latest OS, namely the ability to use a virtual TPM inside Generation 2 (link) Virtual Machines. This virtual TPM isn’t emulated in software and therefore a physical TPM is required in the host device. If your machine doesn’t have a TPM (or if the chip is disabled in your BIOS/UEFI), your VM Security settings might be missing the entire Trusted Platform Module section.
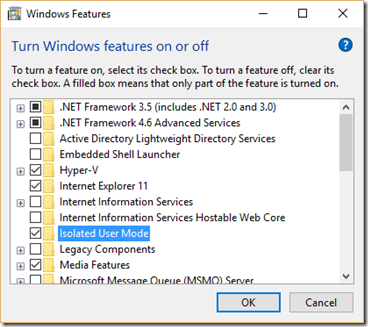
As you can see in the picture, in order to use the virtual TPM in a VM, you’ll first need to enable the Isolated User Mode on your host computer. This can be easily done by turning on the required Windows feature and rebooting.
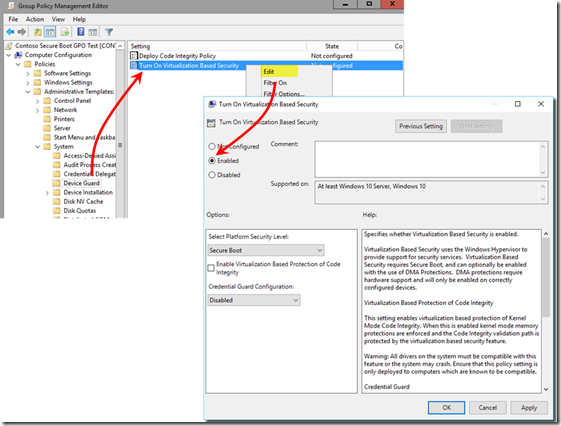
The next step is to turn on Virtualization Based Security using the Local Group Policy Editor (gpedit.msc). Set the policy to Enabled and reboot again.
Last but not least, you need to configure Windows Remote Management on your host machine. Just run winrm quickconfig from an elevated command prompt.
Once you complete the above procedures, you can now enable the virtual TPM in your Generation 2 VMs.
Next post: Sniffing for Passwords with Wireshark
1 comment:
Hello Everyone !
USA SSN Leads/Fullz available, along with Driving License/ID Number with good connectivity.
All SSN's are Tested & Verified.
**DETAILS IN LEADS/FULLZ**
->FULL NAME
->SSN
->DATE OF BIRTH
->DRIVING LICENSE NUMBER
->ADDRESS WITH ZIP
->PHONE NUMBER, EMAIL
->EMPLOYEE DETAILS
*Price for SSN lead $2
*You can ask for sample before any deal
*If you buy in bulk, will give you discount
*Sampling is just for serious buyers
->Hope for the long term business
->You can buy for your specific states too
**Contact 24/7**
Whatsapp > +923172721122
Email > leads.sellers1212@gmail.com
Telegram > @leadsupplier
ICQ > 752822040
Post a Comment